 Prudent IT departments have prepared a comprehensive cybersecurity program as part of their overall Cyber Security Services environment. The program will consist of policies and procedures to be followed by the IT Department itself and by users to minimize the potential loss of intellectual property and attacks from malware and intruders.
Prudent IT departments have prepared a comprehensive cybersecurity program as part of their overall Cyber Security Services environment. The program will consist of policies and procedures to be followed by the IT Department itself and by users to minimize the potential loss of intellectual property and attacks from malware and intruders.
However, as the FBI has pointed out the greatest security threat is not from attacks or malware but sits in the chair facing the screen. Users often view cybersecurity services as a nuisance and an intrusion that prevents him from doing their work and interferes with their entertainment. They will try to work around and subvert security.
The FBI again believe that the majority of hacking attacks and security breaches are not just to make mischief, but to steal intellectual property. Having effective Cyber Security Services is therefore vital to the company, perhaps even to the extent of securing its survival.
Common methods where users subvert security include:
-
Passwords
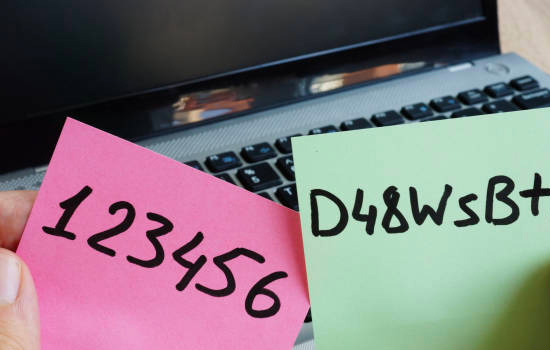
Using easily guessed passwords. Birthdays, car registrations, family names are common. Writing them down in an easily found place. Even to the extent of a Post-It note attached to the monitor. It’s also worth noting that sharing them with friends and colleagues, is a big no-no. In addition, using someone else’s credentials to access applications and data they are not authorised to.
-
External devices

Using flash drives and external hard drives to swap information between home and the office is a prime vector for intellectual property theft. More so, adding devices such as personal laptops and smartphones to the corporate network.
-
Media

Using flash drives and external hard drives to bring media content from home. Home systems are generally not as well protected against malware as are corporate systems. Downloading media content from dubious websites, both at home and at work, is also a culprit.
What can be Done?

It will be difficult in most corporate environments to set up enforcement environments where security infractions are met with punitive measures. The modern vogue for co-operative and holistic work environments and stringent security measures do not sit well together.
It is also important that the IT Department is not perceived as both policeman and judge. They will collect the information identifying security breaches, and if possible identity who is responsible, but it is not their duty to act as judge, jury and possible executioner.
Most organizations now take two main routes towards establishing a Cybersecurity Environment, that of education and training in the need for cybersecurity coupled with technical measures to prevent users from taking adverse actions.
In technical terms, your IT department can introduce several measures over and above the standard anti-malware and network intrusion appliances and software. Most of thee measures will be invisible to users, unless and until they hit a measure intended to preserve the security environment.
Things IT Department can do include:

- Setting up a standard desktop environment, managed centrally. Users cannot change equipment configurations and in particular cannot load their own applications software;
- Disabling the USB ports on the desktop to prevent the use of external storage devices;
- Implementing a password management regime. Users must change passwords at regular intervals. Passwords have minimum standards, a minimum length, a mix of lower and upper case characters, numbers and special characters.
However, the main efforts must be in the area of user education and training.
The first step is to set out clear guidelines for the use of corporate IT resources – a usage policy framework. Users have this explained to them as part of their induction process, and they agree to it every time they log-on to the corporate systems. This is usually expressed in terms of a “Fair Use” policy. It also provides a framework against which activities can be measured and appropriate corrective actions are taken.
Again, as part of the induction process, and with frequent periodic reinforcement, users have the need for security explained to them. The process will include a detailed explanation of the potential threats that lurk in wait, for example, phishing, and why they must do as much as possible to avoid them. Users are made aware of new threats and threat vectors.
Users must also know what to do in the event of an actual or suspected security breach. The process can be set out in the policy document but must be explained again during reinforcement.
To help provide a focus, some organisations have set up security groups, looking something like the old Quality Circles where users discuss security issues and how they can be made more effective and ideally less intrusive.
Technology can only go so far in setting up a cybersecurity services environment. It takes the co-operation and understanding of users to make sure that it is as effective as possible.
